Blogs
As cybersecurity professionals, we encounter many cybersecurity issues, vulnerabilities, and trending threats on a daily basis. In an effort to share this knowledge with those who may find it helpful, we frequently post blogs on these topics. Our goal is to provide valuable information to those who are searching for it.
Hunting Down Remcos RAT: How CrowdStrike Update Mishaps Can Reveal Hidden Threats
Table Of Contents Background Threat Landscape Threat Hunting Importance of Hypothesis in Threat Hunting Methodologies of Hypothesis Based hunting Plan Document IOCs Gathering TTPs Information MITRE Mapping Behavioral Analysis Investigate Mitigate Conclusion Background Recently, the cybersecurity community faced a significant challenge worldwide due to a BSOD (Blue Screen of Death) error caused by a CrowdStrike update.
Read More
leveraging the SQL Injection to Execute the XSS by Evading CSP
Although it sounds silly, I am dumb enough to do this.
Read More
International standard for information security (ISO) - 27001
Table Of Contents ISO 27001 Introduction About ISMS Needs of ISMS How ISO 27001 work?
Read More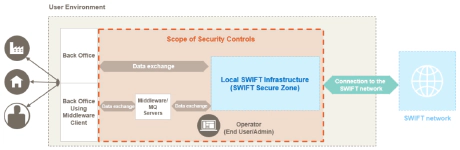
A Pentester's Prespective: SWIFT Vulnerability Assessment
Table Of Contents Local SWIFT Infrastructure Operators Operators PCs Data Exchange Layer Middleware Server Architecture Assessment Approaches Approach - I Approach - II What should a tester look for while using this approach?
Read More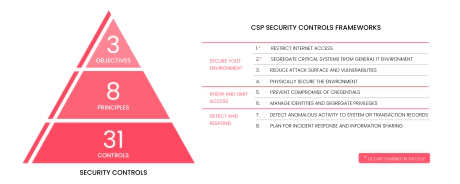
SWIFT CSP v2022 assessment
Table Of Contents SWIFT CSP v2022 assessment Why Is It Required?
Read More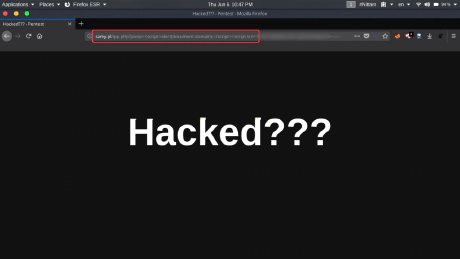
XSS on Samy Pl
In this article, I am going to explain a security issue that I found on a web site which is famous within the information security researchers.
Read More![CVE-2021-3258 | S-XSS to Defacement & Account Takeover [Q2A Themes]](/images/blog/CVE-2021-3258/7th_huefd100b93957c8ceeee9a23a5762cecf_112696_460x0_resize_q100_h2_box_3.webp)
CVE-2021-3258 | S-XSS to Defacement & Account Takeover [Q2A Themes]
In this article, I am going to share a POC (Proof of Concept) on a vulnerability that I found on a popular Forum Management System by Q2A.
Read More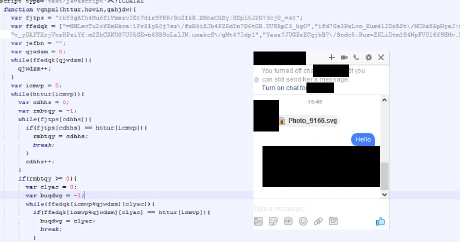
Facebook SVG Locky Ransomware Analysis
This Is What Actually Facebook’s SVG Malware Is Doing. We Had Used W3School’s IDE While Analyzing The Malicious SVG File.
Read More
ByPassing EBay XSS Protection
Hi there, today I want to share small proof of concept regarding “Reflective Cross-Site Scripting [ R-XSS ]” which I had found on eBay back in 2016.
Read More